Comparing a Physical Security Assessment with a Cybersecurity Assessment
A physical security assessment and a cybersecurity assessment
both aim to protect an organization’s assets; however, they focus upon very different
types of risks. A physical security assessment evaluates how well an
organization protects its people, facilities, equipment or physical assets from
real-world threats. Whereas a cybersecurity assessment evaluates how
well an organization protects its digital systems, networks and data from cyber
threats.
A Security Assessment is a critical examination and analysis to:
· Identify risks – existing security-related conditions
· Identify security-related vulnerabilities or deficiencies
· Identify the level of security protection needed
· Make recommendations for improvement
Key Differences in Physical Security and Cybersecurity
|
Physical Security |
Cybersecurity |
|
· Protects buildings and people and assets |
· Protects networks and data |
|
· Focuses on locks, alarms & video cameras |
· Focuses on firewalls & software systems |
|
· Threats are tangible |
· Threats are digital |
|
· Tests physical access |
· Tests system access |
|
|
|
What is Involved in a physical security assessment?
A physical security assessment involves:
§ Facility perimeter security
o Property entry/exit points
o Fences, gates, barriers
o Exterior lighting
o Landscaping
§ Facility Access Control
o Building locks
o Door construction
o Windows and glazing material
o Visitor management procedures
o Electronic access control
§ Internal security measures
o Intrusion detection systems
o Emergency exits and protocols
§ Video Surveillance Systems
o Video surveillance cameras and coverage
o Monitoring of video surveillance systems
o Video surveillance recording and storage
§ Risk and threat analysis
o Identify potential risks and vulnerabilities
o Identify potential threats-theft, intrusion
o Recommendations for improvement
Physical Security Assessment Checklist
1. Perimeter Security
a. Clearly defined property boundaries (fences, walls, natural barriers)
b. Fence conditions (height, gaps, damage, climb resistance)
c. Gates secured (locks, access control, monitored)
d. Vehicle barriers (bollards, crash-rated where needed)
e. Adequate perimeter lighting (no dark spots)
f. Surveillance coverage of perimeter (CCTV placement, blind spots)
g. Signage (restricted access, warnings)
2. Access Control
a. Entry points minimized and controlled
b. Access control systems (badges, keycards, biometrics) functioning properly
c. Visitor management process (sign-in, badges, escorts)
d. Tailgating prevention measures (turnstiles, guards, awareness)
e. Key management procedures (issuance, tracking, revocation)
f. Access levels aligned with roles (least privilege)
3. Surveillance and Monitoring
a. CCCTV coverage for all critical areas
b. Cameras positioned correctly (angles, no obstructions)
c. Recording retention policy defined and enforced
d. Monitoring (live or recorded) assigned to personnel
e. Alarm system installed (instruction detection, motion sensors)
4. Lighting
a. Exterior lighting sufficient for safety and visibility
b. Interior lighting in hallways, stairwells, and storage areas
c. Emergency lighting operational
d. Backup power for critical lighting
5. Building Security
a. Doors and windows secure (locks, reinforced frames)
b. Emergency exits secured by compliant (panic hardware)
c. Roof and utility access points secured
d. Security of HVAC, electrical and utility systems
e. Locking mechanisms regularly inspected
6. Security Personnel
a. Guards trained and licensed (if applicable)
b. Clearly defined roles and responsibilities
c. Patrol routines established and documented
d. Incident reporting procedures followed
e. Communication tools available (radios, phones)
What is involved in a cybersecurity assessment?
A cybersecurity assessment is an evaluation of an organization’s computer systems, networks, and data protection again cyber threats.
· A cybersecurity assessment serves to:
o Identify security gaps and vulnerabilities
o Protect sensitive data
o Reduce the risk of breaches
o Meet legal or regulatory requirements
· A cybersecurity assessment evaluates:
o Systems and infrastructure – computers, servers, networks, cloud services
o Policies and procedures – security rules, access controls, incident response plans
o Vulnerabilities – system weaknesses hackers could exploit
· Types of cybersecurity assessments:
o Vulnerability assessment – scans computer systems to identify weaknesses
o Penetration testing – simulate real attacks
o Risk assessment – Identify threats and estimate potential impact
Cybersecurity Assessment Checklist
1. Define Scope and Objectives
a. Identify systems, networks, applications, and data in scope
b. Define assessment goals (compliance, risk reduction audit, etc.)
c. Determine regulatory requirements (e.g., GDPR, HIPAA, PCI-DSS)
d. Establish rules of engagement (what’s allowed/not allowed)
e. Identify key stakeholders and contacts
2. Asset inventory & Classification
a. Create/update inventory of all assets (serves, endpoints, cloud, apps)
b. Classify data (public, internal, confidential, restricted)
c. Identify critical business systems
d. Map data flows between systems
3. Threat Modeling
a. Identify potential threat actors (insiders, cybercriminals, nation-states)
b. Analyze attack surfaces (network, APIs, endpoints, users)
c. Use frameworks like MITRE ATT&CK
d. Document likely attack scenarios
4. Vulnerability Assessment
a. Run automated vulnerability scans
b. Identify missing patches and outdated software
c. Check for misconfigurations (cloud, firewalls, servers)
d. Review known vulnerabilities (CVEs)
e. Validate findings manually where necessary
5. Penetration Testing
a. Perform controlled exploitation attempts
b. Test web applications (OWASP Top 10)
c. Test network security (internal & external)
d. Assess privilege escalation paths
e. Document successful attack chains
6. Identity & Access Management (IAM)
a. Review user accounts and roles
b. Enforce least privilege principle
c. Check for unused/dormant accounts
d. Verify MFA implementation
e. Audit privileged access
7. Network Security Review
a. Analyze firewall rules and configurations
b. Review network segmentation
c. Check VPN and remote access security
d. Inspect intrusion detection/prevention system (IDS/IPS)
e. Monitor open ports and exposes services
8. Endpoint &System Security
a. Verify endpoint protection (EDR/antivirus))
b. Check system hardening (CIS benchmarks)
c. Review patch management processes
d. Ensure disk encryption is enabled
e. Evaluate logging and monitoring
9. Application Security
a. Perform secure code review (if applicable)
b. Test authentication and session management
c. Validate input handling (prevent injection attacks)
d. Check API security
e. Assess third-party dependencies
10. Data Protection & privacy
a. Ensure encryption (at rest and in transit)
b. Review key management practices
c. Validate backup processes and recovery testing
d. Check data retention and disposal policies
e. Assess compliance with privacy regulations
11. Security Monitoring & Incidental Response
a. Review SIEM/logging solutions
b. Verify alerting and escalation procedures
c. Evaluate incident response plan
d. Conduct tabletop exercises
e. Measure detection and response times
12. Physical Security (if applicable)
a. Control access to facilities and server rooms
b. Use surveillance and monitoring systems
c. Security hardware disposal processes
13. Security Awareness & Training
a. Conduct employee security training
b. Run phishing simulations
c. Evaluate awareness of policies and procedures
14. Third-Party Risk management
a. Assess vendor security posture
b. Review contracts and SLAs for security clauses
c. Monitor third-party access to systems
15. Risk Analysis & Prioritization
a. Assign risk levels (low/medium/high/critical)
b. Evaluate likelihood vs impact
c. Prioritize remediation actions
d. Map risks to business impact
16. Reporting & Remediation Plan
a. Document findings clearly (technical + executive summary)
b. Provide remediation recommendations
c. Assign ownership and timelines
d. Track remediation progress
17. Continuous improvement
a. Schedule regular re-assessments
b. Implement continuous monitoring
c. Update policies and controls
d. Align with frameworks like NIST
CONDUCTING EFFECTIVE SECURITY ASSESSMENTS
CERTIFICATION SEMINAR
The American Crime Prevention Institute (ACPI) has developed a comprehensive crime prevention training program designed to enable participants to effectively conduct a wide range of high quality physical security assessments or surveys.
The course provides specific instruction for identifying risks and vulnerabilities and making recommendations for improvements in existing facilities, campuses and communities. Anyone involved in securing businesses, residences, communities, institutions and other facilities will benefit from this program.
Individuals who participate in and successfully complete this training program will be recognized as Certified Security Assessment Specialists.
To learn more and register click here.
ACPI is the worldwide leader in enabling law enforcement
agencies, businesses, institutions, and security professionals to reduce
criminal activity and risk and enhance quality of life through the delivery of
practical, unbiased training and certification programs. Visit our website at acpionline.com to learn about our
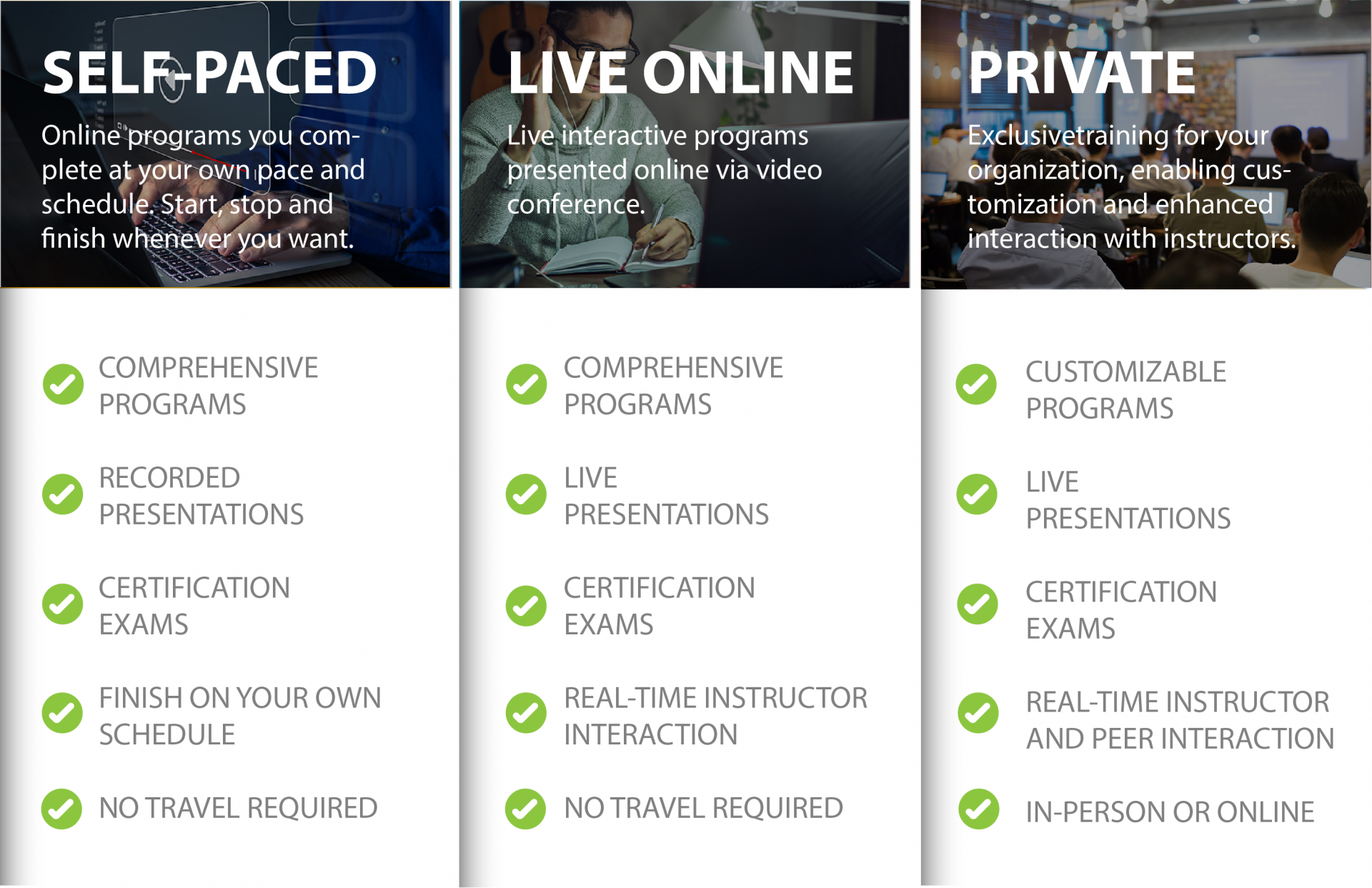
comprehensive list of both live virtual and self-paced training courses.
Join our newsletter!
Which format is right for you?